AliExpress Wiki
API Access Management: The Ultimate Guide to Secure, Scalable, and Efficient API Control
Master API access management for secure, scalable API control in modern development. Learn how to enforce authentication, authorization, rate limiting, and monitoringessential for IoT, embedded systems, and cloud integrations using tools like the CP2112 Debug Board and Arduino.
Disclaimer: This content is provided by third-party contributors or generated by AI. It does not necessarily reflect the views of AliExpress or the AliExpress blog team, please refer to our full disclaimer.
People also searched
Related Searches
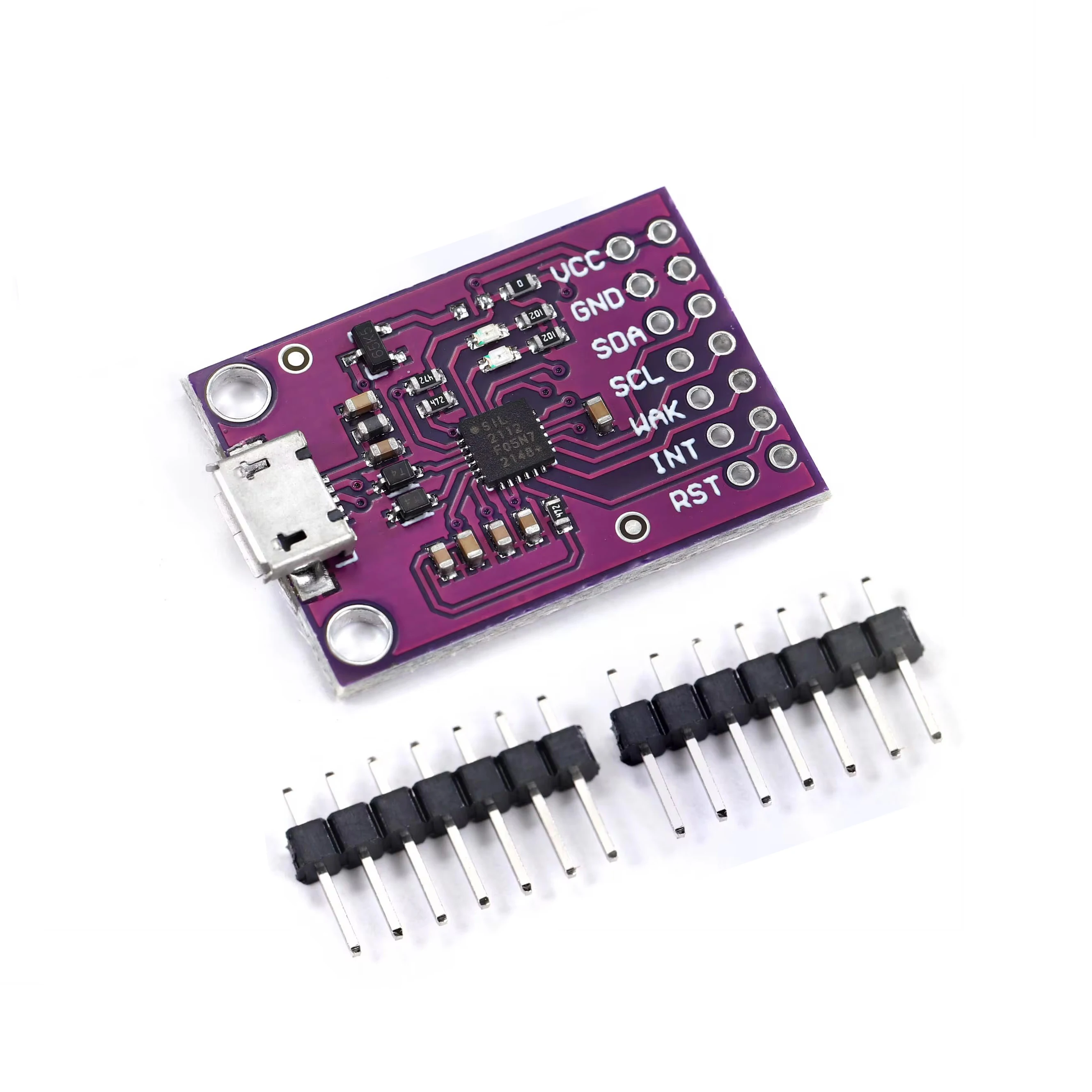
<h2> What Is API Access Management and Why Does It Matter in Modern Development? </h2> <a href="https://www.aliexpress.com/item/1005004252794090.html"> <img src="https://ae-pic-a1.aliexpress-media.com/kf/S37828e222b764d3f83b1c74ea56076ca0.jpg" alt="BMP390 BMM350 BMI323 Ten-axis IMU Module"> </a> API access management is a critical component of modern software architecture, serving as the gatekeeper for how applications, services, and users interact with your digital resources. At its core, API access management refers to the process of controlling who can access an API, what actions they can perform, and under what conditions. This includes authentication, authorization, rate limiting, logging, and monitoring. In today’s interconnected digital ecosystemwhere microservices, cloud platforms, and IoT devices dominateAPIs are the backbone of communication between systems. Without proper access management, these APIs become vulnerable to abuse, data breaches, and performance degradation. For developers and system architects working with embedded systems, sensor integration, or IoT devices, API access management takes on a more specialized form. Consider the CP2112 Debug Board USB to SMBus I2C Communication Module, a popular product on AliExpress used for interfacing with sensors like the CCS811. While this hardware is not a traditional API gateway, it plays a crucial role in enabling secure, controlled communication between microcontrollers and external devicesessentially managing access to hardware-level data streams. The CP2112 chip acts as a bridge, translating USB signals into I2C/SMBus protocols, ensuring that only authorized commands are passed through. This is a form of low-level API access management: controlling how software communicates with physical hardware. In broader terms, API access management ensures that only authenticated and authorized users or systems can invoke specific endpoints. For example, when a mobile app requests environmental data from a sensor network, the API access management system verifies the app’s identity, checks its permissions, and enforces usage limits. This prevents unauthorized access, protects sensitive data, and maintains system stability. Without such controls, a single misconfigured device or malicious actor could flood the system with requests, leading to denial-of-service scenarios. Moreover, API access management supports scalability. As your application growsfrom a single sensor node to a network of thousands of devicesthe need for centralized control becomes paramount. Tools like OAuth 2.0, JWT tokens, and API keys are standard mechanisms used to manage access. These are often integrated into development kits like the CP2112 Evaluation Kit, which allows developers to test secure communication protocols before deploying in real-world environments. The importance of API access management extends beyond security. It enables analytics and monetization. By tracking who uses which API endpoints and how frequently, businesses can gain insights into user behavior, identify high-value customers, and even implement usage-based billing models. For instance, a smart home platform might charge premium users for real-time air quality data from CCS811 sensors, with access controlled via API keys tied to user subscriptions. In the context of AliExpress, where developers and hobbyists source hardware like the CP2112 Debug Board, API access management is not just a backend concernit’s a foundational element of the entire development workflow. When you purchase a module that supports secure communication protocols, you’re investing in a system that inherently respects access control principles. This ensures that your projects, whether for personal experimentation or commercial deployment, are built on a secure and reliable foundation. Ultimately, API access management is not a luxuryit’s a necessity. Whether you're managing cloud APIs, IoT device networks, or embedded hardware interfaces, the ability to control access is what separates a robust, scalable system from a chaotic, insecure one. As technology evolves, so too must our approach to access control, ensuring that every interaction, from the smallest I2C transaction to the largest enterprise API call, is secure, traceable, and governed by clear policies. <h2> How to Choose the Right API Access Management Solution for Your Project? </h2> <a href="https://www.aliexpress.com/item/1005005475737714.html"> <img src="https://ae-pic-a1.aliexpress-media.com/kf/S539fdfec809c4230bdead54b6880404ce.jpg" alt="1~10PCS EGBO CP2112 Debug Board USB to SMBus I2C Communication 2.0 Micro USB Evaluation Kit for CCS811 Sensor Module for arduino"> </a> Selecting the right API access management solution depends on your project’s scale, complexity, security requirements, and technical stack. For developers working with hardware like the CP2112 Debug Board USB to SMBus I2C Communication Module, the choice isn’t always about enterprise-grade API gatewaysit’s about ensuring that the underlying communication protocols support secure, controlled access from the ground up. First, consider the environment in which your API will operate. If you're building a small-scale IoT prototype using an Arduino and a CCS811 sensor module, you may not need a full-fledged API management platform like Kong or Apigee. Instead, focus on hardware and firmware-level access control. The CP2112 Evaluation Kit, for example, provides a secure bridge between USB and I2C, allowing developers to implement access control logic directly in the microcontroller code. This includes validating command sequences, limiting read/write frequency, and authenticating data requestsessentially creating a lightweight API access layer at the device level. Next, evaluate the authentication and authorization mechanisms supported by your tools. Does your development kit support secure key exchange? Can you embed API keys or tokens into the firmware? The CP2112 module, when paired with an Arduino, enables developers to implement token-based access control by requiring a specific handshake sequence before allowing data transmission. This mimics the behavior of higher-level API gateways but operates at the hardware level, making it ideal for resource-constrained environments. Another critical factor is scalability. If your project is intended to grow from a single sensor node to a distributed network of hundreds of devices, you’ll need a solution that can scale without compromising security. In such cases, consider integrating your hardware with cloud-based API management platforms. For example, you could use AWS API Gateway or Azure API Management to control access to data collected by multiple CP2112-equipped sensors. This allows you to define roles, enforce rate limits, and monitor usage across the entire networkall from a centralized dashboard. Security is also paramount. Look for solutions that support encryption (TLS/SSL, audit logging, and threat detection. The CP2112 module supports secure communication via I2C, but additional layers of encryption should be implemented in the application layer. For instance, you can encrypt sensor data before transmission and validate digital signatures to prevent tampering. Finally, consider ease of integration and developer experience. A good API access management solution should offer clear documentation, SDKs, and compatibility with popular development environments. The CP2112 Evaluation Kit is designed for quick prototyping with Arduino, which means it integrates seamlessly with existing workflows. This reduces the learning curve and accelerates developmentkey advantages when choosing a solution for both hobbyists and professionals. In summary, choosing the right API access management solution isn’t about picking the most complex toolit’s about aligning the solution with your project’s needs. For hardware-focused projects, prioritize solutions that support secure, low-level communication and can scale into cloud-based systems. The CP2112 Debug Board, with its robust USB-to-I2C interface and compatibility with Arduino, exemplifies a hardware platform that enables effective access control from the ground up. <h2> How Does API Access Management Differ from API Security and API Gateway? </h2> <a href="https://www.aliexpress.com/item/1005008297578590.html"> <img src="https://ae-pic-a1.aliexpress-media.com/kf/S4a0b932981684f2687842f2987b908d6j.jpg" alt="Tuya 5000User 5In Touch Lcd 2MP Camera Biometric Face Recognition Wifi Fingerprint Access Control Time Attendance Free Cloud API"> </a> While API access management, API security, and API gateway are often used interchangeably, they represent distinct but interconnected concepts in the API lifecycle. Understanding the differences is crucial for building a robust, secure, and efficient systemespecially when working with hardware like the CP2112 Debug Board USB to SMBus I2C Communication Module. API access management focuses specifically on controlling who can access an API and what they’re allowed to do. It involves authentication (verifying identity, authorization (granting permissions, rate limiting, and session management. For example, when an Arduino device using the CP2112 module sends a request to read data from a CCS811 sensor, access management determines whether the request is valid, who made it, and whether the device has permission to perform that action. API security, on the other hand, is a broader concept that encompasses all measures taken to protect APIs from threats. This includes encryption (e.g, TLS for data in transit, input validation to prevent injection attacks, protection against DDoS, and secure key storage. While access management is a key part of API security, it doesn’t cover everything. For instance, even if access is properly managed, a poorly secured API endpoint could still be vulnerable to SQL injection or data leakage. An API gateway is a software layer that sits between clients and backend services, acting as a reverse proxy. It handles tasks like routing, load balancing, caching, andyesaccess management. However, an API gateway is not the same as access management. It’s a tool that can implement access management, but it’s not the concept itself. Think of the API gateway as the door and access management as the security system that controls who gets through and what they can do once inside. In the context of embedded systems, the distinction becomes even clearer. The CP2112 module doesn’t act as a full API gatewayit’s a communication bridge. But it can be used to implement access control logic at the hardware level. For example, the microcontroller can reject unauthorized I2C commands or limit how often a sensor can be read. This is a form of access management, but it’s not a gateway. It’s a lightweight, hardware-based enforcement mechanism. Moreover, while API gateways are typically cloud-based and designed for large-scale enterprise use, access management can be implemented at any leveldevice, network, or application. This makes it highly adaptable. For a hobbyist using the CP2112 Evaluation Kit, implementing access control in firmware is often more practical than setting up a cloud gateway. In summary, API access management is about control, API security is about protection, and an API gateway is a tool that can support both. When building projects with hardware like the CP2112 module, you can leverage all three: use the hardware to enforce basic access rules, implement encryption for security, and integrate with a cloud gateway for scalability. Understanding these differences allows you to design a layered, resilient system that meets your project’s unique needs. <h2> What Are the Best Practices for Implementing API Access Management in Embedded Systems? </h2> <a href="https://www.aliexpress.com/item/1005009534898252.html"> <img src="https://ae-pic-a1.aliexpress-media.com/kf/S51d843e821654a08bf2aa07257234220h.jpg" alt="CP2112 Debug Board USB to SMBus I2C Communication Module 2.0 MicroUSB 2112 Evaluation Kit for CCS811 Sensor Module for arduino"> </a> Implementing API access management in embedded systems requires a balance between security, performance, and simplicityespecially when working with resource-constrained devices like those using the CP2112 Debug Board USB to SMBus I2C Communication Module. Unlike cloud-based APIs, embedded systems often lack the processing power and memory to run complex authentication frameworks. Therefore, best practices must be tailored to the hardware’s capabilities. First, implement strong authentication at the device level. Use unique identifiers or cryptographic keys embedded in the firmware to authenticate each device. For example, when an Arduino communicates with a CCS811 sensor via the CP2112 module, the microcontroller can verify that the sensor responds only to known, authorized devices. This prevents unauthorized hardware from accessing the data stream. Second, enforce rate limiting to prevent abuse. Even if a device is authenticated, it should not be allowed to flood the system with requests. Implement simple counters in the firmware to limit how often a sensor can be read or a command can be sent. This protects against both accidental overuse and malicious attacks. Third, use secure communication protocols. The CP2112 module supports I2C and SMBus, which are inherently low-level and not encrypted. To enhance security, implement encryption in the application layersuch as AES-128before transmitting data. This ensures that even if the communication is intercepted, the data remains protected. Fourth, enable logging and monitoring. While embedded devices may not have full logging capabilities, they can still record access attempts, errors, and anomalies. Store this data locally or send it to a central server for analysis. This helps detect suspicious behavior and supports forensic investigations. Fifth, keep firmware updated. Vulnerabilities in the CP2112 driver or Arduino code can be exploited if not patched. Regularly update your software and use secure boot mechanisms to ensure only trusted code runs on the device. Finally, design for scalability. Even if your project starts small, plan for growth. Use modular code that can integrate with cloud-based API management platforms later. This allows you to transition from local access control to centralized management as your system expands. By following these best practices, you can build embedded systems that are not only functional but also secure and future-proof. <h2> How Can I Compare API Access Management Tools for Hardware Development Projects? </h2> <a href="https://www.aliexpress.com/item/1005008295924179.html"> <img src="https://ae-pic-a1.aliexpress-media.com/kf/S2a2e298cefd94507af2344cc58da3248u.jpg" alt="Asia Teco World Debut 5inch 5000user TCP/IP WIFI Tuya App Dynamic Face Recognition Access Control Attendance Machine Fingerprint"> </a> When comparing API access management tools for hardware development, focus on compatibility, security, ease of use, and scalability. For projects involving the CP2112 Debug Board and Arduino, tools that integrate seamlessly with existing development environments are ideal. Look for solutions that support Arduino libraries, offer clear documentation, and provide secure key management. Compare features like authentication methods (API keys, OAuth, JWT, rate limiting, logging, and support for encryption. Also consider whether the tool can scale from a single device to a network of sensors. Tools that support both local and cloud-based access control offer the most flexibility. Ultimately, the best tool is one that fits your project’s size, security needs, and technical expertise.