AliExpress Wiki
Linux Hacking: The Ultimate Guide to Style, Skill, and Subculture
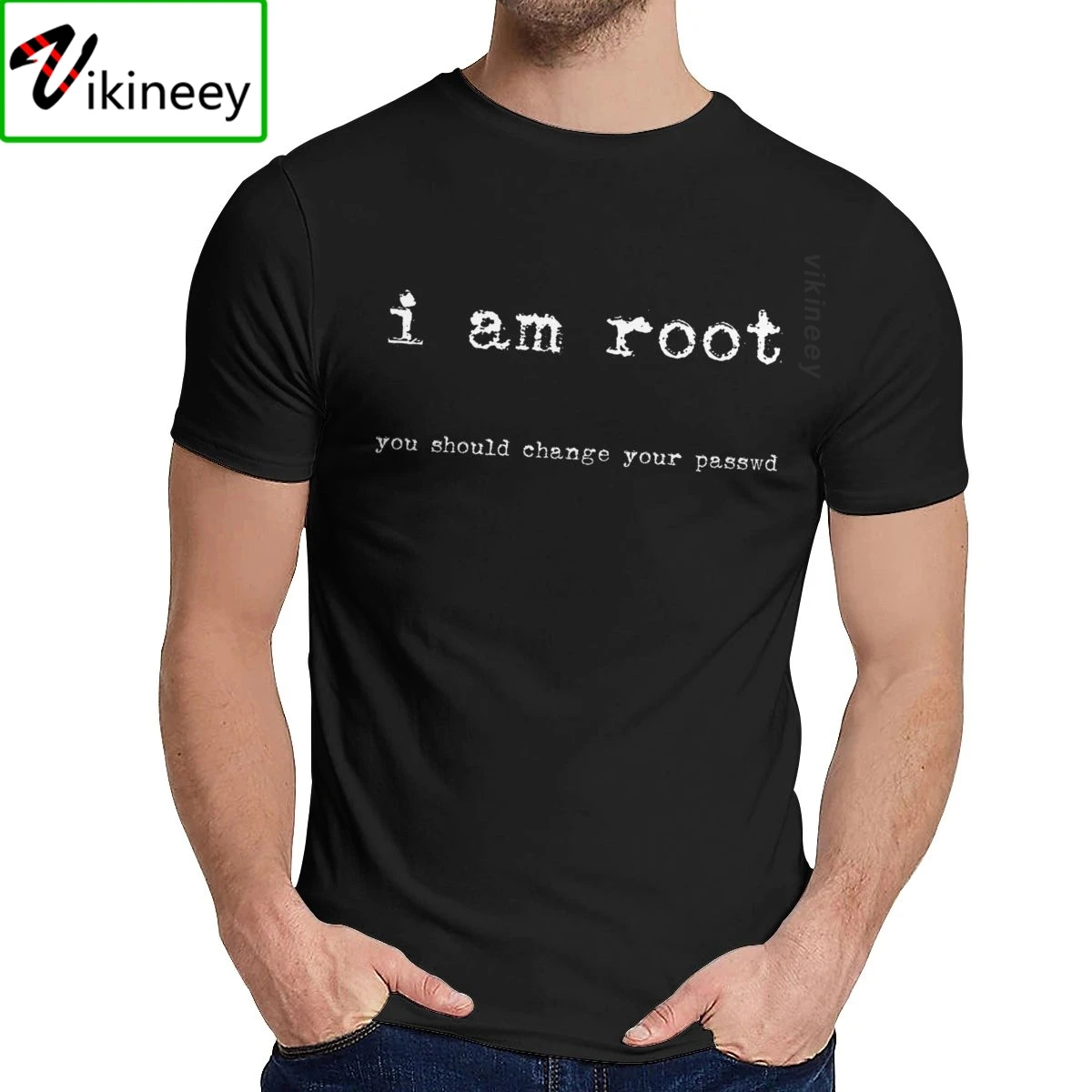
Discover the true spirit of Linux hacking: a culture of curiosity, control, and open-source empowerment. Beyond coding, it’s about mastering the terminal, understanding system depth, and embracing digital freedom. Wear your identity with iconic I Am Root shirtssymbols of technical mastery and hacker pride.
Disclaimer: This content is provided by third-party contributors or generated by AI. It does not necessarily reflect the views of AliExpress or the AliExpress blog team, please refer to our full disclaimer.
People also searched
Related Searches
<h2> What Is Linux Hacking and Why Is It More Than Just Coding? </h2> <a href="https://www.aliexpress.com/item/1005002955321689.html"> <img src="https://ae-pic-a1.aliexpress-media.com/kf/H5072d5c6ab194491ba23a0e5166a6846W.jpg" alt="AWUS036NH Kali Network Card Cdlinux Ubuntu Drive-free USB Wireless Penetration Network Card"> </a> Linux hacking isn’t about breaking into systems or violating cybersecurity lawsit’s a cultural and technical movement rooted in open-source philosophy, problem-solving, and deep system understanding. At its core, Linux hacking refers to the practice of mastering Linux operating systems through command-line proficiency, system customization, and ethical exploration of how software and hardware interact. It’s a mindset embraced by developers, system administrators, security researchers, and tech enthusiasts who value transparency, control, and innovation. The term “hacking” often carries a negative connotation in mainstream media, but in the Linux community, it’s synonymous with creativity, curiosity, and empowerment. When someone says “I’m hacking Linux,” they’re usually referring to automating tasks, building custom environments, optimizing performance, or exploring the inner workings of the OS through terminal commands. This is where tools like Bash, Zsh, Vim, Git, and systemd come into playeach a weapon in the hacker’s arsenal. This subculture has grown into a global community, with forums, conferences, and even fashion statements celebrating the ethos of Linux hacking. One of the most iconic symbols? The “I Am Root” T-shirt. This simple yet powerful design declares a user’s identity: someone who has command-line access, understands system privileges, and respects the power of the terminal. The phrase “I Am Root” is not just a boastit’s a badge of honor for those who’ve earned their way into the heart of Linux. On platforms like AliExpress, you’ll find a surge in popularity for shirts like the “O-neck I Am Root Ubuntu Command Line Linux Unix Hacking T-shirt.” These aren’t just garmentsthey’re wearable declarations of belonging. Made from natural cotton and designed for unisex comfort, these tees appeal to both seasoned hackers and newcomers eager to join the movement. The design often features the iconic “root” prompt, terminal syntax, or Unix/Linux command-line snippets, turning everyday fashion into a conversation starter. But why does this matter? Because Linux hacking isn’t just about technical skillit’s about identity. In a world where most users interact with technology through GUIs and apps, the Linux hacker stands apart. They choose to see the machine not as a black box, but as a canvas. They prefer the terminal over the mouse, configuration files over click-through wizards, and self-reliance over dependency. The rise of these T-shirts reflects a broader trend: the merging of technical expertise with personal expression. People don’t just want to use Linuxthey want to wear it. The “I Am Root” shirt isn’t just a piece of clothing; it’s a manifesto. It says, “I understand the system. I can control it. I am not afraid of the command line.” Moreover, the popularity of such items on AliExpress highlights the global reach of the Linux community. From students in India learning Bash scripts to developers in Brazil customizing their Ubuntu environments, the demand for Linux-themed apparel is growing. These shirts are not nichethey’re part of a larger cultural shift toward valuing knowledge, autonomy, and digital literacy. So when you see someone wearing a Linux hacking T-shirt, don’t assume they’re a cybercriminal. They’re likely a passionate technologist, a curious learner, or a proud member of a community that believes in open access, transparency, and the power of code. And if you’re considering joining them, the first step might just be putting on a shirt that says, “I Am Root.” <h2> How to Choose the Best Linux Hacking T-Shirt for Your Style and Identity? </h2> <a href="https://www.aliexpress.com/item/1005007539876921.html"> <img src="https://ae-pic-a1.aliexpress-media.com/kf/Se299bbeb777b497ebd6721316a3aa8aeU.jpg" alt="Fenvi T919 1750Mbps PCIe Desktop Wifi Card BCM94360 For MacOS Hackintosh 802.11AC Bluetooth 4.0 Dual Band Wireless Adapter Win10"> </a> Choosing the perfect Linux hacking T-shirt goes beyond just picking a designit’s about aligning your personal style with your technical identity. With countless options on AliExpress, from minimalist command-line prints to bold “I Am Root” statements, it’s essential to evaluate each shirt based on material, fit, design meaning, and community resonance. First, consider the fabric. The “O-neck I Am Root Ubuntu Command Line Linux Unix Hacking T-shirt” is often made from 100% natural cotton, which offers breathability, softness, and comfortideal for long coding sessions or tech meetups. Natural cotton also appeals to eco-conscious buyers who value sustainable fashion. Look for shirts labeled as “organic cotton” or “GOTS-certified” if environmental impact is a priority. Avoid polyester blends if you want a premium feel and better durability. Next, assess the fit and cut. The term “unisex” suggests a versatile design, but not all unisex shirts are created equal. Some are slim-fit, others are relaxed or oversized. If you’re into a streetwear aesthetic, an oversized cut with a bold terminal font might suit you. If you prefer a clean, professional look, a classic crew neck with a subtle “root@localhost” message could be more appropriate. Try to match the shirt’s silhouette to your everyday wardrobewhether you lean toward casual, geek-chic, or minimalist. Design is where personal identity shines. A shirt with a complex command-line sequence like sudo rm -rf might appeal to those who appreciate dark humor and technical irony. But if you’re more into elegance, a simple “I Am Root” in monospace font with a subtle Linux penguin (Tux) logo could be a better fit. Some designs even include ASCII art of terminal prompts or shell scripts, turning the shirt into a wearable piece of code. Another factor is authenticity. Is the design created by a real Linux enthusiast or just a generic template? Look for shirts with accurate terminal syntax, correct Linux commands, and references to real tools likegrep, awk,ssh, or vim. Misused commands or incorrect syntax can signal a lack of technical credibilitysomething that matters in the hacker community. Also, consider the brand or seller. On AliExpress, many sellers offer similar designs, but quality varies. Check reviews for details on print durability, color accuracy, and shrinkage after washing. A shirt that fades after one wash defeats the purpose of a long-term statement piece. Finally, think about the community. Wearing a Linux hacking shirt isn’t just about fashionit’s about belonging. If you attend hackathons, Linux user groups, or tech conferences, your shirt becomes a conversation starter. A well-chosen design can spark connections with like-minded individuals. For example, a shirt with “Ubuntu” in the title might attract fellow Ubuntu users, while one with “Unix” could resonate with older-school system admins. Ultimately, the best Linux hacking T-shirt is one that reflects your journey. Whether you’re a beginner learninglsandcd, or an advanced user scripting automation with Python and Bash, your shirt should mirror your level of expertise and passion. It’s not just clothingit’s a badge of honor, a symbol of your digital identity, and a way to say, “I speak the language of the machine.” <h2> Why Is the “I Am Root” Phrase So Iconic in the Linux Hacking Community? </h2> <a href="https://www.aliexpress.com/item/1005009367073855.html"> <img src="https://ae-pic-a1.aliexpress-media.com/kf/H2453f2c90bb4402d9dbe5b86990cf8ae3.jpg" alt="Ruby Power Hoodies Long Sleeve Geek Computer Program Ruby Script Programming Linux Programmer Hack Hacker Ror Ruby On"> </a> The phrase “I Am Root” is more than a sloganit’s a cultural cornerstone in the Linux and open-source world. Root is the superuser account in Linux systems, the one with unrestricted access to every file, command, and process. When a user types sudo su or logs in as root, they’re stepping into the highest level of system control. Saying “I Am Root” is a declaration of power, responsibility, and technical mastery. But it’s not just about privilegeit’s about philosophy. In the Linux community, “root” symbolizes freedom. It means you’re not bound by default settings, pre-installed software, or vendor lock-in. You’re in charge. You can modify the kernel, recompile the OS, or delete a file with a single command. This level of control is rare in modern computing, where most users are confined to GUIs and app stores. The phrase “I Am Root” also carries a sense of irony and humor. It’s often used in a playful way, especially in memes and T-shirt designs. For example, a shirt that says “I Am Root” with a terminal prompt in the background is both a joke and a statement: “Yes, I have root access. And yes, I know what I’m doing.” It’s a way for hackers to laugh at the power they wieldwithout taking it too seriously. This phrase has deep roots in Unix history. The term “root” dates back to the earliest versions of Unix, where the superuser was named “root” because it was the foundation of the system. Over time, it became a symbol of the hacker ethos: curiosity, independence, and a willingness to dig deep. Today, it’s used not just by system administrators, but by developers, security researchers, and even students learning Linux for the first time. On AliExpress, the “I Am Root” T-shirt has become a bestseller because it taps into this cultural significance. It’s not just a piece of clothingit’s a statement of identity. When someone wears it, they’re saying, “I understand Linux. I’ve used the terminal. I’ve run sudo commands. I’m not afraid of the system.” It’s a badge of honor in a community that values knowledge over popularity. Moreover, the phrase resonates with the broader hacker movement. From the early days of the MIT AI Lab to modern-day open-source projects, the idea of being “root” has represented autonomy and innovation. It’s a reminder that technology should be accessible, transparent, and under the user’s controlnot hidden behind layers of abstraction. The popularity of this phrase also reflects a growing interest in digital self-sovereignty. In an age of surveillance, data harvesting, and platform dependency, many people are turning to Linux as a way to reclaim control. The “I Am Root” shirt becomes a symbol of resistanceagainst closed systems, against corporate control, against the idea that you need permission to use your own computer. Even in fashion, the phrase has become a design staple. It’s used in minimalist typography, retro terminal-style fonts, and even as part of larger ASCII art. Some shirts pair “I Am Root” with other hacker phrases like “sudo make me a sandwich” or “There’s no place like /home,” creating a full-on geek aesthetic. Ultimately, “I Am Root” is more than a commandit’s a mindset. It represents the belief that you don’t need to be told how to use your computer. You can learn, explore, and control it. And if you wear a shirt that says “I Am Root,” you’re not just dressing the partyou’re living it. <h2> How Does Linux Hacking Differ from General Programming or Cybersecurity? </h2> <a href="https://www.aliexpress.com/item/1005009364702829.html"> <img src="https://ae-pic-a1.aliexpress-media.com/kf/H269bceb95c6c407480dd12a7c9259adbT.jpg" alt="Ruby Power Tank Tops Vest Sleeveless Geek Computer Program Ruby Script Programming Linux Programmer Hack Hacker Ror Ruby On"> </a> While Linux hacking, programming, and cybersecurity are often grouped together in tech discussions, they represent distinct domains with unique goals, tools, and mindsets. Understanding the differences is crucial for anyone looking to specialize or express their identity through fashion like the “I Am Root” T-shirt. Programming is about writing code to solve problemswhether it’s building a website, developing an app, or automating a workflow. It focuses on syntax, logic, and software design. A programmer might use Python, JavaScript, or Java to create functional applications. Their success is measured by clean code, efficient algorithms, and working features. Cybersecurity, on the other hand, is about protecting systems from threats. It involves identifying vulnerabilities, preventing breaches, and responding to attacks. Cybersecurity professionals use tools like Wireshark, Metasploit, and Nmap to scan networks, detect malware, and secure infrastructure. Their work is defensive, focused on risk mitigation and compliance. Linux hacking sits at the intersection of bothbut with a unique twist. It’s not just about writing code or defending systems. It’s about mastering the operating system itself. A Linux hacker doesn’t just use the terminalthey live in it. They understand how processes run, how permissions work, how the kernel manages memory, and how services are started and stopped. For example, a programmer might write a script to back up files. A Linux hacker would go further: they’d write the script, test it in a container, set up cron jobs, secure the script with proper permissions, and monitor it with journalctl. They’d also know how to debug issues usingdmesg, strace, orlsof. This deep system knowledge is what sets Linux hacking apart. It’s not about building appsit’s about understanding the machine. It’s about knowing that chmod 700 gives a file only root access, or that sudo temporarily elevates privileges. It’s about recognizing that ~.bashrc is where your shell environment is customized. The “I Am Root” T-shirt reflects this distinction. It’s not a programmer’s shirtit’s a system-level thinker’s shirt. It says, “I don’t just use Linux. I control it.” It’s a statement of technical depth, not just coding ability. Moreover, Linux hacking often involves ethical exploration. Unlike malicious hacking, it’s about learning how systems worknot breaking them. This includes reverse engineering, analyzing system logs, and experimenting with configurations in safe environments. In contrast, general programming and cybersecurity are more specialized. A cybersecurity expert might focus on penetration testing, while a programmer might specialize in web development. But a Linux hacker is a generalist with deep system fluency. This is why Linux hacking shirts are so popular among developers, IT pros, and students. They’re not just fashionthey’re a declaration of a unique skill set. They say, “I understand the OS. I can navigate the terminal. I know what root means.” And in a world where most people are passive users, that’s a powerful identity to wear proudly.