AliExpress Wiki
What is an SSH Server and How to Use It for Secure Data Access?
An SSH server ensures secure remote access to systems and data through encrypted communication, ideal for managing industrial hardware like hard disk circuit boards. It authenticates users via cryptographic keys or passwords, preventing unauthorized access. AliExpress offers compatible industrial accessories, enabling efficient, secure data management for professionals handling sensitive operations.
Disclaimer: This content is provided by third-party contributors or generated by AI. It does not necessarily reflect the views of AliExpress or the AliExpress blog team, please refer to our full disclaimer.
People also searched
Related Searches
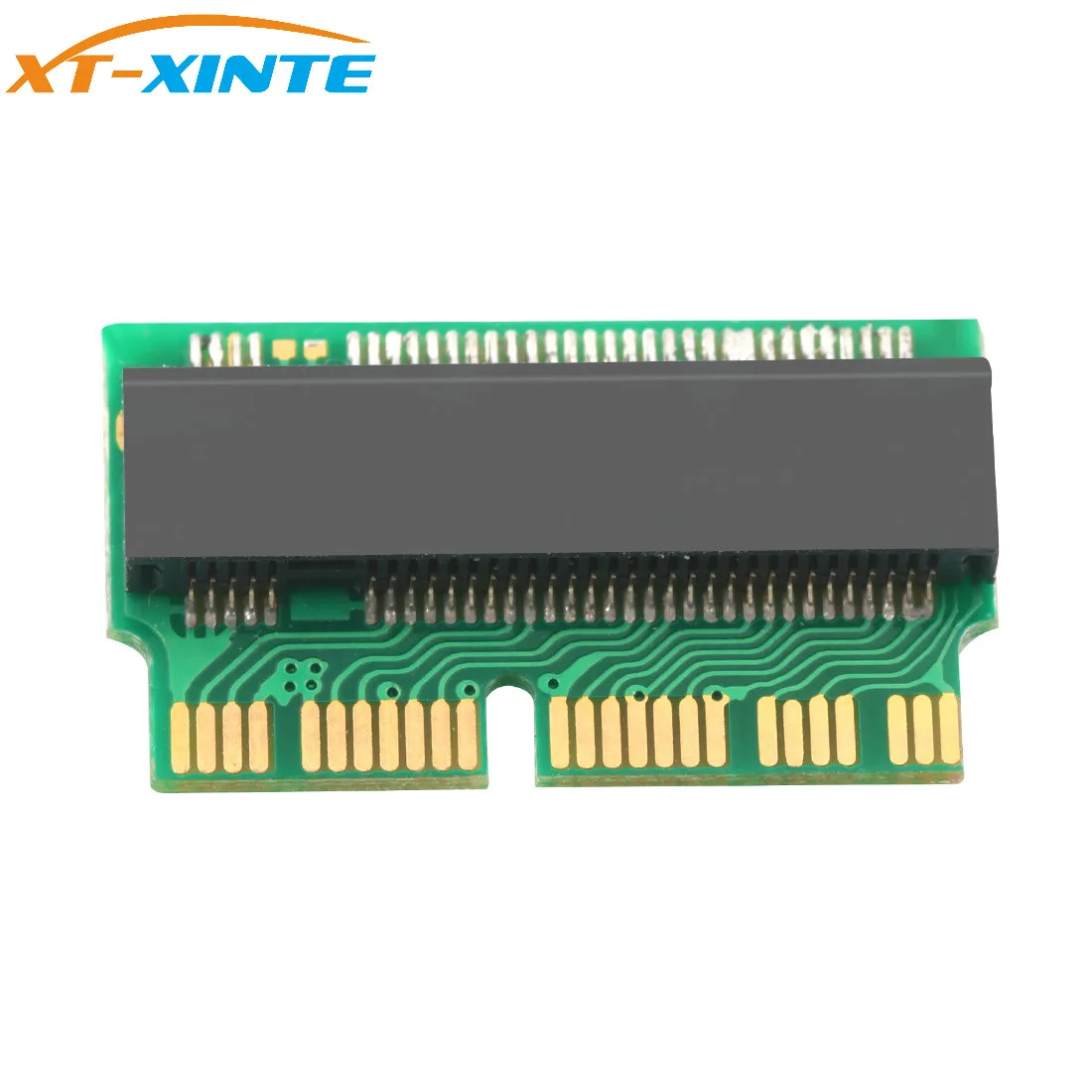
<h2> What is an SSH Server and How Does It Work? </h2> An SSH server (Secure Shell server) is a critical tool for securely accessing and managing remote systems over unsecured networks. It uses cryptographic protocols to encrypt data transmitted between the client and server, ensuring confidentiality and integrity. SSH servers are widely used in IT infrastructure, cloud computing, and DevOps workflows to execute commands, transfer files, and manage configurations remotely. The core functionality of an SSH server revolves around authentication and encryption. When a user connects to an SSH server, they must authenticate using a username and password, a public/private key pair, or other methods like multi-factor authentication. Once authenticated, the server establishes an encrypted tunnel for communication, preventing eavesdropping and tampering. This makes SSH servers indispensable for tasks like remote server administration, secure file transfers (via SFTP, and automated deployment pipelines. For users looking to implement an SSH server, the first step is to choose a reliable hardware or cloud-based solution. If you're setting up a physical server, ensure your hardware supports secure protocols and has sufficient processing power to handle encryption tasks. For cloud environments, platforms like AWS, Google Cloud, or Azure offer pre-configured SSH server instances. When selecting hardware or cloud services, consider factors like scalability, compatibility with your operating system, and ease of integration with existing tools. AliExpress offers a range of networking and server-related accessories that can enhance your SSH server setup. For example, high-quality SSDs and storage adapters ensure fast data access and reliable performance, which is crucial for servers handling heavy workloads. Products like the M Key M.2 PCIe X4 for NGFF AHCI 2280 SSD 12+16Pin Adapter Card are ideal for upgrading storage in systems like MacBook Pro or MacPro, ensuring your SSH server operates efficiently even under high demand. <h2> How to Set Up an SSH Server on Your Computer or Network? </h2> Setting up an SSH server involves several steps, from installing the necessary software to configuring security settings. The process varies slightly depending on your operating system, but the general workflow remains consistent. On Linux systems, the most common SSH server is OpenSSH. To install it, use your distribution’s package manager (e.g, sudo apt install openssh-server for Ubuntu. After installation, configure the SSH daemon by editing the /etc/ssh/sshd_configfile. Key settings include the port number (default is 22, allowed authentication methods, and access restrictions. Once configured, restart the SSH service withsudo systemctl restart sshdand test the connection using an SSH client. For Windows users, OpenSSH is available as part of the Windows Subsystem for Linux (WSL) or through third-party tools like PuTTY. Enable the OpenSSH server feature via the Control Panel, configure the settings in thesshd_configfile, and start the service. Ensure your firewall allows traffic on the SSH port to avoid connection issues. When setting up an SSH server, prioritize security. Disable password authentication in favor of key-based authentication to reduce brute-force attack risks. Generate strong SSH keys using tools likessh-keygen and store them securely. Additionally, consider changing the default SSH port to a non-standard number to deter automated scans. AliExpress provides essential hardware components that can streamline your SSH server setup. For instance, high-speed SSDs and reliable network adapters ensure your server maintains optimal performance. The M Key M.2 PCIe X4 for NGFF AHCI 2280 SSD 12+16Pin Adapter Card is compatible with MacBooks and MacPros, making it an excellent choice for users who need to integrate SSH servers into Apple ecosystems. <h2> What Are the Best Practices for Securing an SSH Server? </h2> Securing an SSH server is critical to protect sensitive data and prevent unauthorized access. While SSH itself is a secure protocol, misconfigurations or weak authentication methods can introduce vulnerabilities. One of the most effective practices is to disable password authentication and use key-based authentication instead. This eliminates the risk of brute-force attacks and ensures only users with the correct private key can access the server. Generate strong 4096-bit RSA or Ed25519 keys and store them in a secure location. Regularly rotate keys and revoke any that are no longer in use. Another key step is to restrict access to specific users or groups. In the sshd_config file, use the AllowUsers or AllowGroups directive to limit who can connect. This reduces the attack surface by preventing unauthorized users from attempting to log in. Additionally, consider implementing rate-limiting rules using tools like fail2ban to block IP addresses that make repeated failed login attempts. Regularly updating your SSH server software is essential to address security patches and vulnerabilities. Set up automated updates for your operating system and SSH packages to ensure you’re always running the latest versions. Monitor server logs for suspicious activity and configure alerts for failed login attempts or unusual behavior. AliExpress offers hardware solutions that can enhance the security of your SSH server. For example, high-quality SSDs with built-in encryption provide an additional layer of protection for stored data. The M Key M.2 PCIe X4 for NGFF AHCI 2280 SSD 12+16Pin Adapter Card ensures fast and secure data access, making it ideal for servers handling sensitive information. <h2> How to Choose the Right SSH Server for Your Specific Use Case? </h2> Selecting the right SSH server depends on your specific needs, whether you’re managing a small business network, deploying applications in the cloud, or running a personal development environment. For small-scale use, OpenSSH is often sufficient due to its simplicity and widespread support. It’s pre-installed on most Linux and macOS systems, making it easy to set up and manage. If you need advanced features like port forwarding or tunneling, OpenSSH’s configuration options provide flexibility. For enterprise environments, consider commercial SSH server solutions like Bitvise or MobaXterm. These tools offer enhanced security features, centralized management, and integration with Active Directory. They’re ideal for organizations that require granular access controls and audit trails. Cloud-based SSH servers are another option, especially for teams working remotely. Platforms like AWS EC2 or Google Cloud Compute Engine provide pre-configured SSH instances that can be scaled on demand. These services often include built-in security features like automatic patching and intrusion detection. When choosing hardware for your SSH server, prioritize performance and reliability. High-speed SSDs, such as the M Key M.2 PCIe X4 for NGFF AHCI 2280 SSD 12+16Pin Adapter Card, ensure fast data access and reduce latency. For Apple users, this adapter is compatible with MacBook Air 2013-2015 and MacPro models, making it a versatile choice for integrating SSH servers into Apple ecosystems. <h2> What Are the Common Issues with SSH Servers and How to Troubleshoot Them? </h2> Despite their robustness, SSH servers can encounter issues like connection failures, authentication errors, or performance bottlenecks. Understanding common problems and their solutions is essential for maintaining a reliable server. One frequent issue is the Connection refused error, which typically indicates that the SSH service isn’t running or the port is blocked by a firewall. Verify the SSH service status with systemctl status sshd and ensure the correct port is open in your firewall settings. If you’re connecting to a remote server, double-check the IP address and port number. Authentication errors often stem from incorrect key permissions or mismatched usernames. Ensure your private key has 600 permissions chmod 600 ~.ssh/id_rsa) and that the public key is correctly added to the~.ssh/authorized_keysfile on the server. If you’re using password authentication, confirm that thePasswordAuthentication yesline is present in thesshd_config file. Performance issues like slow connections can be caused by outdated software or network congestion. Upgrade your SSH server to the latest version and optimize your network settings. For hardware-related bottlenecks, consider upgrading to faster storage solutions like the M Key M.2 PCIe X4 for NGFF AHCI 2280 SSD 12+16Pin Adapter Card, which ensures efficient data transfer and reduces latency. By addressing these common issues and leveraging high-quality hardware from AliExpress, you can ensure your SSH server operates smoothly and securely.